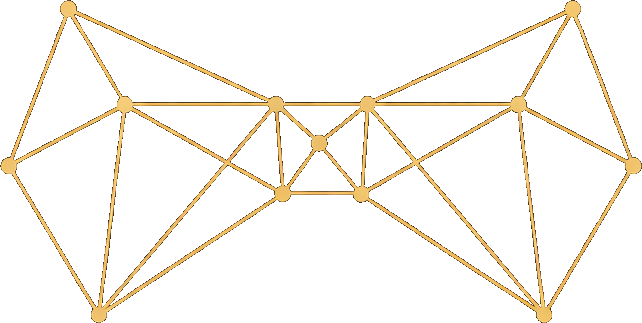
Part of Alfred’s six-layer architecture. The Agentic layer hosts the specialists that do the work.
Your team
Alfred runs five specialists that work continuously on your vault. Each one has a defined role, a strict scope, and no ability to exceed its permissions — even if the underlying language model tries.| Specialist | What they do | When they work |
|---|---|---|
| Curator | Reads what you share and creates structured vault records | Automatically when new content arrives |
| Janitor | Scans for broken links, missing metadata, orphaned records — and repairs them | Periodic sweeps |
| Distiller | Surfaces assumptions, decisions, constraints, contradictions, and synthesized insights | On-demand or scheduled |
| Surveyor | Embeds records as vectors, clusters by meaning, labels clusters, writes relationship links | On-demand or scheduled |
| Clerk | Stateless LLM worker dispatched by other specialists for analytical tasks — classifying inputs, extracting entities, writing summaries | On-demand by other specialists |
OpenClaw — the agent runtime
OpenClaw is Alfred’s AI agent gateway. It manages sessions, skills, device pairing, and agent execution. Every specialist runs through OpenClaw, which provides a consistent interface to the LLM backends you’ve configured. OpenClaw binds to localhost and is reachable externally only via Cloudflare Tunnel (outbound-only from your server — your IP is never exposed).Scope enforcement
Each specialist operates within strictly defined permissions, enforced in code before every vault operation. The language model cannot bypass these rules.| Specialist | Create | Read | Edit | Delete |
|---|---|---|---|---|
| Curator | Entity types | All | All | Never |
| Janitor | Never | All | All | Yes |
| Distiller | Learning types only | All | Never | Never |
The vault CLI gate
Agents never touch the filesystem directly. Every vault operation goes through thealfred vault CLI, which mediates all access:
- Scope checking — is this specialist allowed to perform this operation?
- Path validation — is this file inside the vault boundary? (blocks
../, symlinks, escapes) - Schema validation — is this a valid record type with correct frontmatter?
- Mutation logging — every create, edit, delete, and move is recorded in an append-only audit trail
Prompt injection defense
No AI system can guarantee 100% immunity to prompt injection. Alfred’s approach is defense in depth — even if the language model is tricked, the damage it can do is bounded by technical enforcement that the model cannot override.
| Layer | Enforcement | What it does |
|---|---|---|
| Scope | Code | Operations outside the specialist’s scope are blocked |
| Path validation | Code | File access outside the vault boundary is rejected |
| Schema validation | Code | Invalid record types and status values are rejected |
| Mutation logging | Code | Every change is recorded in an append-only audit trail |
| Skill instructions | Prompt | Each specialist receives explicit behavioral constraints |
Third-party access
Your Alfred connects only to configured LLM providers, Hetzner S3 (for backups), Tailscale, and Cloudflare. No third-party plugins (ClawHub installation is disabled by default), no arbitrary API access, no browser extensions. The attack surface is deliberately minimal.Your Specialists
Monitor and direct your specialists
Device Pairing
Manage OpenClaw device access
Security
Full threat model and sandboxing details